» książki » Computers - Security - General
 |
Networks, Security and Complexity: The Role of Public Policy in Critical Infrastructure Protection
ISBN: 9781843769521 / Angielski / Twarda / 160 str. Termin realizacji zamówienia: ok. 5-8 dni roboczych. In 1997, for his doctoral dissertation in public policy from George Mason University, Gorman (public policy, George Mason U.) began constructing a map of all the interdependent telecommunications and information technology networks, gas pipelines, railroad systems, and electric power lines in the US. After 9-11, he extended that effort to assist th
In 1997, for his doctoral dissertation in public policy from George Mason University, Gorman (public policy, George Mason U.) began constructing a map...
|
cena:
530,25 |
 |
Cyber Security: Economic Strategies and Public Policy Alternatives
ISBN: 9781847203557 / Angielski / Twarda / 288 str. Termin realizacji zamówienia: ok. 5-8 dni roboczych. Cyberspace is the nervous system of today's advanced economies, linking critical infrastructures across public and private institutions. The authors of this book comprehensively explore the many issues surrounding this unique system, including private sector cyber security investment decisions and implementation strategies, public policy efforts to ensure overall security, and government's role in the process.
Cyberspace is the nervous system of today's advanced economies, linking critical infrastructures across public and private institutions. The authors o...
|
cena:
593,25 |
 |
Information Risk and Security: Preventing and Investigating Workplace Computer Crime
ISBN: 9780566086854 / Angielski / Twarda / 362 str. Termin realizacji zamówienia: ok. 5-8 dni roboczych. Information Risk and Security explains the complex and diverse sources of risk for any organization and provides clear guidance and strategies to address these threats before they happen, and to investigate them, if and when they do. Edward Wilding focuses particularly on internal IT risk, workplace crime, and the preservation of evidence, because it is these areas that are generally so mismanaged. There is advice on: preventing computer fraud, IP theft and systems sabotage adopting control and security measures that do not hinder business operations but which effectively block criminal...
Information Risk and Security explains the complex and diverse sources of risk for any organization and provides clear guidance and strategies to addr...
|
cena:
773,06 |
 |
Power and Security in the Information Age: Investigating the Role of the State in Cyberspace
ISBN: 9780754670889 / Angielski / Twarda / 182 str. Termin realizacji zamówienia: ok. 5-8 dni roboczych. The marriage of computers and telecommunications, the global integration of these technologies and their availability at low cost is bringing about a fundamental transformation in the way humans communicate and interact. But however much consensus there may be on the growing importance of information technology today, agreement is far more elusive when it comes to pinning down the impact of this development on security issues. Written by scholars in international relations, this volume focuses on the role of the state in defending against cyber threats and in securing the information age. The...
The marriage of computers and telecommunications, the global integration of these technologies and their availability at low cost is bringing about a ...
|
cena:
773,06 |
 |
The Holistic Operational Readiness Security Evaluation: HORSE Project Series: Governance Documentation and Information Technology Security Policies De
ISBN: 9781468063875 / Angielski / Miękka / 512 str. Termin realizacji zamówienia: ok. 5-8 dni roboczych. Holistic Operational Readiness Security Evaluation - HORSE Project Series Volume 1 is the professional companion book to the popular global resource, the HORSE Project Wiki, that provides a comprehensive examination of corporate information technology and security governance documents ranging from a corporate charter, policies and standards. This book provides a holistically approachable road map to design, ratification, implementation and maintenance of corporate security program policies. The guidance contained within has been the bedrock for corporate governance within some of the biggest...
Holistic Operational Readiness Security Evaluation - HORSE Project Series Volume 1 is the professional companion book to the popular global resource, ...
|
cena:
189,47 |
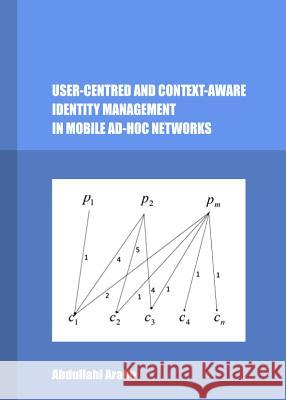 |
User-Centred and Context-Aware Identity Management in Mobile Ad-Hoc Networks
ISBN: 9781443847964 / Angielski / Twarda / 185 str. Termin realizacji zamówienia: ok. 5-8 dni roboczych. The emergent notion of ubiquitous computing makes it possible for mobile devices to communicate and provide services via networks connected in an ad-hoc manner. These have resulted in the proliferation of wireless technologies such as Mobile Ad-hoc Networks (MANets), which offer attractive solutions for services that need flexible setup as well as dynamic and low cost wireless connectivity. However, the growing trend outlined above also raises serious concerns over Identity Management (IM) due to a dramatic increase in identity theft. The problem is even greater in service-oriented...
The emergent notion of ubiquitous computing makes it possible for mobile devices to communicate and provide services via networks connected in an ad-h...
|
cena:
209,95 |
 |
Intrusion Detection in Wireless Ad-Hoc Networks
ISBN: 9781466515659 / Angielski / Twarda / 258 str. Termin realizacji zamówienia: ok. 5-8 dni roboczych. Presenting cutting-edge research, Intrusion Detection in Wireless Ad-Hoc Networks explores the security aspects of the basic categories of wireless ad-hoc networks and related application areas. Focusing on intrusion detection systems (IDSs), it explains how to establish security solutions for the range of wireless networks, including mobile ad-hoc networks, hybrid wireless networks, and sensor networks. This edited volume reviews and analyzes state-of-the-art IDSs for various wireless ad-hoc networks. It includes case studies on honesty-based intrusion detection systems,...Presenting cutting-edge research, Intrusion Detection in Wireless Ad-Hoc Networks explores the security aspects of the basic categories of w... |
cena:
523,69 |
 |
Shields Up: Complete Guide to Windows Security and Mac Privacy
ISBN: 9781470120917 / Angielski / Miękka / 160 str. Termin realizacji zamówienia: ok. 5-8 dni roboczych. Is your computer really safe? Are you sure your privacy is protected online? "Shields Up Complete Guide to Windows Security and Mac Privacy" will arm you with fundamental knowledge to stay safe both online and offline. With "Shields Up " you will:
Is your computer really safe? Are you sure your privacy is protected online? "Shields Up Complete Guide to Windows Security and Mac Privacy" will... |
cena:
123,49 |
 |
Handbook of Remote Biometrics: For Surveillance and Security
ISBN: 9781447126706 / Angielski / Miękka / 381 str. Termin realizacji zamówienia: ok. 5-8 dni roboczych. The development of technologies for the identi?cation of individuals has driven the interest and curiosity of many people. Spearheaded and inspired by the Bertillon coding system for the classi?cation of humans based on physical measurements, scientists and engineers have been trying to invent new devices and classi?cation systems to capture the human identity from its body measurements. One of the main limitations of the precursors of today's biometrics, which is still present in the vast majority of the existing biometric systems, has been the need to keep the device in close contact with...
The development of technologies for the identi?cation of individuals has driven the interest and curiosity of many people. Spearheaded and inspired by...
|
cena:
610,90 |
 |
Security Engineering for Cloud Computing: Approaches and Tools
ISBN: 9781466621251 / Angielski / Twarda / 258 str. Termin realizacji zamówienia: ok. 5-8 dni roboczych. Security Engineering for Cloud Computing: Approaches and Tools provides a theoretical and academic description of Cloud security issues, methods, tools and trends for developing secure software for Cloud services and applications. This book is a comprehensive collection including a wide range of existing problems and challenges that would be useful in both the academic and research world.
Security Engineering for Cloud Computing: Approaches and Tools provides a theoretical and academic description of Cloud security issues, methods, tool...
|
cena:
1018,47 |
 |
Innovations in Digital Watermarking Techniques
ISBN: 9783642260384 / Angielski / Miękka / 186 str. Termin realizacji zamówienia: ok. 5-8 dni roboczych. This book introduces a number of digital watermarking techniques. It contains the latest research into the digital watermarking techniques in the artificial intelligence environment. The book is directed to those interested in the area of information security.
This book introduces a number of digital watermarking techniques. It contains the latest research into the digital watermarking techniques in the arti...
|
cena:
407,25 |
 |
Secure IP Mobility Management for VANET
ISBN: 9783319013503 / Angielski / Miękka / 106 str. Termin realizacji zamówienia: ok. 5-8 dni roboczych. This brief presents the challenges and solutions for VANETs' security and privacy problems occurring in mobility management protocols including Mobile IPv6 (MIPv6), Proxy MIPv6 (PMIPv6), and Network Mobility (NEMO). The authors give an overview of the concept of the vehicular IP-address configurations as the prerequisite step to achieve mobility management for VANETs, and review the current security and privacy schemes applied in the three mobility management protocols. Throughout the brief, the authors propose new schemes and protocols to increase the security of IP addresses within VANETs...
This brief presents the challenges and solutions for VANETs' security and privacy problems occurring in mobility management protocols including Mobile...
|
cena:
203,61 |
 |
Transactions on Large-Scale Data- and Knowledge-Centered Systems IX
ISBN: 9783642400681 / Angielski / Miękka / 123 str. Termin realizacji zamówienia: ok. 5-8 dni roboczych. The LNCS journal Transactions on Large-Scale Data- and Knowledge-Centered Systems focuses on data management, knowledge discovery, and knowledge processing, which are core and hot topics in computer science. Since the 1990s, the Internet has become the main driving force behind application development in all domains. An increase in the demand for resource sharing across different sites connected through networks has led to an evolution of data- and knowledge-management systems from centralized systems to decentralized systems enabling large-scale distributed applications providing high...
The LNCS journal Transactions on Large-Scale Data- and Knowledge-Centered Systems focuses on data management, knowledge discovery, and knowledge proce...
|
cena:
203,61 |
 |
Transactions on Large-Scale Data- And Knowledge-Centered Systems X: Special Issue on Database- And Expert-Systems Applications
ISBN: 9783642412202 / Angielski / Miękka / 201 str. Termin realizacji zamówienia: ok. 5-8 dni roboczych. The LNCS journal Transactions on Large-Scale Data- and Knowledge-Centered Systems focuses on data management, knowledge discovery, and knowledge processing, which are core and hot topics in computer science. Since the 1990s, the Internet has become the main driving force behind application development in all domains. An increase in the demand for resource sharing across different sites connected through networks has led to an evolution of data- and knowledge-management systems from centralized systems to decentralized systems enabling large-scale distributed applications providing high...
The LNCS journal Transactions on Large-Scale Data- and Knowledge-Centered Systems focuses on data management, knowledge discovery, and knowledge proce...
|
cena:
203,61 |
 |
Research in Attacks, Intrusions, and Defenses: 16th International Symposium, Raid 2013, Rodney Bay, St. Lucia, October 23-25, 2013, Proceedings
ISBN: 9783642412837 / Angielski / Miękka / 476 str. Termin realizacji zamówienia: ok. 5-8 dni roboczych. This book constitutes the proceedings of the 16th International Symposium on Research in Attacks, Intrusions and Defenses, former Recent Advances in Intrusion Detection, RAID 2013, held in Rodney Bay, St. Lucia in October 2013. The volume contains 22 full papers that were carefully reviewed and selected from 95 submissions, as well as 10 poster papers selected from the 23 submissions. The papers address all current topics in computer security ranged from hardware-level security, server, web, mobile, and cloud-based security, malware analysis, and web and network privacy.
This book constitutes the proceedings of the 16th International Symposium on Research in Attacks, Intrusions and Defenses, former Recent Advances in I...
|
cena:
203,61 |
 |
Network Intrusion Analysis: Methodologies, Tools, and Techniques for Incident Analysis and Response
ISBN: 9781597499620 / Angielski / Miękka / 252 str. Termin realizacji zamówienia: ok. 5-8 dni roboczych. Nearly every business depends on its network to provide information services to carry out essential activities, and network intrusion attacks have been growing increasingly frequent and severe. When network intrusions do occur, it's imperative that a thorough and systematic analysis and investigation of the attack is conducted to determine the nature of the threat and the extent of information lost, stolen, or damaged during the attack. A thorough and timely investigation and response can serve to minimize network downtime and ensure that critical business systems are maintained in full... Nearly every business depends on its network to provide information services to carry out essential activities, and network intrusion attacks have ... |
cena:
174,51 |
 |
How to Spot Scams Online: First Edition
ISBN: 9781466330580 / Angielski / Miękka / 50 str. Termin realizacji zamówienia: ok. 5-8 dni roboczych. If you are not familiar with online scams, you should read this entire book carefully. This book will teach you how to spot and avoid con-artists. Scams are growing more and more each prevalent day. This book will help you fight scams. Instead of becoming a victim of it, This book will inform you on where to report a scam if you come across one. It will also teach you the five major scams that are going on in today's world as we speak. This book is a life saver.
If you are not familiar with online scams, you should read this entire book carefully. This book will teach you how to spot and avoid con-artists. Sca...
|
cena:
90,67 |
 |
Tunnel Und Verdeckte Kanäle Im Netz: Grundlagen, Protokolle, Sicherheit Und Methoden
ISBN: 9783834816405 / Niemiecki / Miękka / 179 str. Termin realizacji zamówienia: ok. 5-8 dni roboczych. Dass Netzwerkdaten eingebettet in andere Daten (Tunneling) gesendet werden, ist ein Grundprinzip des heutigen Internets. Ob im bisherigen Internet Protocol oder in der kommenden Version, in Transport- oder Anwendungsprotokollen: ohne Tunneling ist der Betrieb moderner Netzwerke nur eingeschrankt moglich. Neben Grundlagen, Protokollen und Fragen der Sicherheit beim Tunneling wird in dem Band auch die verdeckte Netzwerkkommunikation erlautert. Sie ist eine Form der Datenubertragung, bei der der Kommunikationsprozess an sich verborgen bleibt."
Dass Netzwerkdaten eingebettet in andere Daten (Tunneling) gesendet werden, ist ein Grundprinzip des heutigen Internets. Ob im bisherigen Internet Pro...
|
cena:
152,21 |
 |
Image Encryption Scheme Based on Chaotic Maps
ISBN: 9783848484904 / Angielski / Miękka / 92 str. Termin realizacji zamówienia: ok. 5-8 dni roboczych. A new encryption scheme using dynamical 8 x 8 S-box, based on the composition of chaotic maps, is proposed. In this method, the dynamical S-box, one first uses a known chaotic dynamical system to generate a sequence of pseudo-random bytes, then applies certain permutations to them, using the discretized version of another two dimensional chaotic map. A sequence of pseudo-random bytes generated from two dimensional cat map is used to index the entry of the S-box. The output 8 bits (0-255) of the S-box are XOR-ed with the plaintext to obtain the ciphertext and XOR-ed with the ciphertext to...
A new encryption scheme using dynamical 8 x 8 S-box, based on the composition of chaotic maps, is proposed. In this method, the dynamical S-box, one f...
|
cena:
221,75 |
 |
Network Robustness Under Large-Scale Attacks
ISBN: 9781461448594 / Angielski / Miękka / 41 str. Termin realizacji zamówienia: ok. 5-8 dni roboczych. Network Robustness under Large-Scale Attacks provides the analysis of network robustness under attacks, with a focus on large-scale correlated physical attacks. The book begins with a thorough overview of the latest research and techniques to analyze the network responses to different types of attacks over various network topologies and connection models. It then introduces a new large-scale physical attack model coined as area attack, under which a new network robustness measure is introduced and applied to study the network responses. With this book, readers will learn the necessary...
Network Robustness under Large-Scale Attacks provides the analysis of network robustness under attacks, with a focus on large-scale correlated ...
|
cena:
203,61 |













